Test YourEmail & Web Defences
Deliver real-world malware replications via email and web to discover what reaches your users. Validate your defences with 800+ payloads across 100+ file types.
Real-World Threat Emulation
Our payloads mirror the techniques, file types, and delivery methods used by real threat actors and malware strains, giving you the most realistic test of your email and web defences.
Why Choose delivr.to?
Empower your security team with data-driven insights
Validate Posture
Take a data-driven approach to improving your email and web security. Use our growing suite of 800+ payloads to demonstrate exactly what threats can land in your inbox, and in what condition.
Highlight Gaps
Test attachments, links, and inline payloads to assess sandboxing and safe-link controls, then use our tailored insights to prioritise remediation.
Stay Ahead of Threats
Emulate the latest offensive tradecraft, from Adversary-in-the-Middle to callback phishing. Tailor custom campaigns to test everything from CEO impersonation to gift card scams.
How It Works
Test your email and web defences safely, continuously and autonomously.
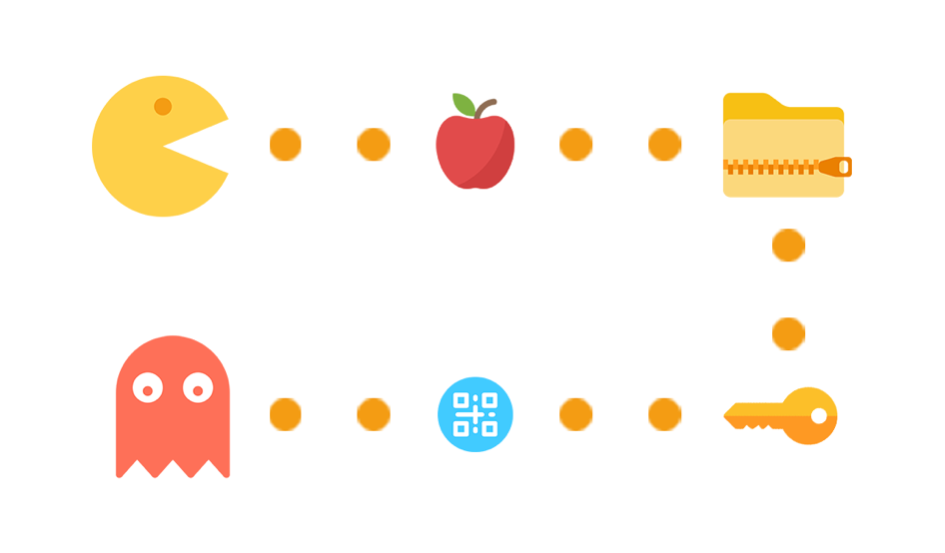
Select Your Payloads
Choose from our library of real-world threat emulations based on the attack techniques, file types, or threat actors you want to test against.
- Target specific threat actor TTPs
- Emulate prevalent malware strains
- Select weaponised file types (SVG, PDF, ZIP, etc.)
- Use curated templates for common scenarios
Deliver Your Payloads
Send payloads to test mailboxes via email or host them for browser-based download. delivr.to handles realistic formatting and proper delivery for both channels.
- Email delivery with attachment, link, or inline methods
- Web delivery for browser-based download testing
- Schedule or launch immediately
- Configure hands-off repeating campaigns
Automated Assessment
Our suite of integrations detect what landed, and in what condition, as well as what was blocked or quarantined. Works for both email and web delivery campaigns.
- Real-time delivery detection
- Browser download monitoring and verification
- Attachment and link rewriting verification
- Alert collection from security tools
Track Results Over Time
Build a comprehensive picture of your email and web security posture. Compare results across campaigns, measure improvement and demonstrate return on investment.
- Historical trend analysis
- Campaign comparison reports
- Threat technique coverage gaps
- Executive-ready dashboards
Built for Security Professionals
Whether you're defending, attacking, or consulting - we've got you covered
Security Teams
Integrate with your Microsoft 365 and Google mailboxes, and security tools likes Microsoft Defender 365 and Sublime Security, to automatically record what payloads landed in your inbox, and in what condition. Want to confirm links were rewritten and active content was stripped? We can provide the answer.
Learn morePurple Teams
Your one-stop shop for payload emulation. Find safe and accurate replications of the latest attack techniques, including zip smuggling & polyglot files, and test your defences across email and web. Visit our research blog.
Learn moreConsultants
Deliver more value to your clients with detailed deliverability tracking and actionable insights. Our automated recommendations help you identify gaps in email and web security controls, while team collaboration features let you share templates and results across engagements.
Learn moreSimple, Transparent Pricing
Choose the plan that fits your security testing needs
Starter
Our most cost-effective plan. 10 downloads and 100 emails a day, perfect for no-frills email and web security validation.
- 100 emails a day
- 10 payload downloads a day
Premium
Unlimited integrations, tailored insights & recommendations, and 2000 emails a day for a comprehensive view of your email and web security posture.
- 2000 emails a day
- Unlimited payload downloads
Enterprise
All you can eat everything, plus Team collaboration, custom payloads & templates, full rebranding, and tailored onboarding.
- Unlimited emails
- Unlimited downloads
Frequently Asked Questions
Common questions about email security testing with delivr.to
Purple teaming combines offensive and defensive security testing. For email, it means sending real threat payloads through your production mail infrastructure to measure what actually reaches users' inboxes. This validates your email security controls against techniques used by real threat actors, rather than relying on theoretical assessments or simulated attacks.
Traditional phishing simulation tools send safe replicas to test user behaviour. delivr.to sends real payload file types and delivery techniques through your production email gateway to test your technical controls. The platform measures whether payloads are blocked, quarantined, or delivered, giving you ground-truth data on your email defence effectiveness.
The platform includes 800+ pre-built payloads across 100+ file types, mapped to MITRE ATT&CK techniques. These cover HTML smuggling, SVG smuggling, WebAssembly smuggling, macro-enabled documents, script files, archive containers, QR code phishing, credential harvesting, and more. All payloads are modelled on real threat actor tradecraft observed in the wild.
delivr.to integrates with Microsoft 365 and Gmail for automatic delivery status tracking, Microsoft Defender 365 for detection correlation, and Sublime Security for detection rule development and testing. A REST API is available for integration with SOAR platforms and custom tooling.
Yes. Payloads are designed to test your defences without causing harm. They trigger the same detection mechanisms as real threats but do not execute malicious actions. You control which email addresses receive payloads, and all campaigns are logged with full audit trails. Campaigns can be sent to validated addresses that you own.
You can run your first campaign within minutes of signing up. Connect your mailbox (Microsoft 365 or Gmail), select payloads from the library, choose your target email address, and launch a campaign. Results are tracked automatically, showing which payloads were delivered, blocked, or quarantined.
Our Research
Insights and analysis from the delivr.to team on the latest phishing techniques, payload delivery, and email and web security trends
About Us
Launched in 2023, we're dedicated to empowering individuals and organisations across the globe with the tools they need to test and enhance their email and web security.

James has a decade of experience delivering attack simulation and purple teaming services, and has spoken on the topic at conferences such as Blackhat, Defcon & TROOPERS. He was also a member of the UK Armed Force's Joint Cyber Unit.
Not sure which plan is right for you?
Let's chat! We'll find the best solution for your security testing needs.